Today I’m publishing a guide that I hope will help improve your personal online security. This guide focuses on the basics – how to reduce the life-altering risks we face as we navigate the internet.
This is a Cyber Security survival guide. I’m going to start by giving you a clear picture of the current state of Cyber Security. Then I’m going to prioritize what you should be protecting. I’m going to focus on the biggest risks and I will explain how to reduce the risk for each category.
If you find this useful, please go ahead and share it extensively.
Current State of Cyber Security
Would you believe it if I told you that there’s a 66% chance that your data has already been stolen and will be stolen again and again? Unfortunately, it doesn’t matter whether you use secure passwords, two-factor authentication, are young or old, or which websites you visit or businesses you do business with. At various points in your life, your data will be stolen. And in all likelihood, it will be stolen repeatedly.
Today, 64% of Americans have already had their data stolen through data breaches. That is almost 2 out of three people.
In the past 3 years we saw the first data breach of more than 1 billion user accounts with the Yahoo breach. That breach affected 1 in 7 people on our planet! In the United States, the OPM breach included the data of our top spies, including their fingerprints and personal data. Even our intelligence services can’t protect highly confidential personnel data.
Data has been stolen from private companies, intelligence agencies and the military. Even cyber security companies have had their data stolen.
How Data Is Stolen
Even if you use a strong password, two factor authentication and best practices for security, your data will still be stolen because the companies whose services you use in some cases will fail to protect their own networks and systems.
How to Prioritize What to Protect
If data breaches are the new normal and if you accept the premise that they are inevitable and unavoidable, the problem we need to solve in our personal and business lives becomes “How do I reduce the risk and the impact of a breach?”
It’s helpful to start this conversation by trying to prioritize what we need to protect. I’m focusing on the really important, upper level things and this is my prioritized list so it’s possible your list could be in a different order.
- Information about us that could help criminals target us in the real world.
- Our financial means – savings accounts, ability to borrow, and our assets.
- Sensitive personal information – medical records, tax data and other private data.
- Our ability to earn an income through our reputation and our ability to provide products or services to people.
Preventing Criminals from Targeting Us in the Real World
In most of the developed countries, it is rare to hear stories of real-world targeting of individuals through information they have ‘leaked’ into the cyber realm. But in developing countries where there’s a greater disparity of wealth, or if you happen to be a superstar or athlete in a developed country, it might be good to:
- Never show high value items (like jewelry or cars) online.
- Share your location in general terms, and if you want to share a specific location, do it after you have left that location.
- Don’t share information that may indicate when or how much you’ve been paid.
- Consider making social profiles only available to people you have approved.
- If you work for someone or some entity with access to highly confidential information, avoid disclosing who your employer is and what your job title is. This includes public websites like LinkedIn.
Protecting Your Financial Means
I’m not concerned with credit card fraud in this section. That risk falls on the vendor and transactions can be reversed. Instead, I’m focused on the kind of risk that can have a permanent impact on your financial well-being.
If an attacker is able to authorize a wire transfer from your savings account, they can empty your bank account and the funds may never be recoverable. This risk applies to savings accounts, checking accounts and investments like brokerage accounts and money market accounts.
If they are able to borrow in your name, it can permanently damage your credit score and your ability to borrow money to buy a home, for example.
I suggest taking the following steps to reduce the risk of large scale financial fraud:
- Make a list of savings and investment accounts. Audit each account to determine how you prove your identity when transferring funds and get a clear idea of what an attacker would need to do to commit fraud on each account.
- Implement any additional security provided by your banks or brokerages:
- callback to a predetermined number.
- authorization from multiple parties prior to transferring funds.
- two factor or hardware-based authentication.
- limiting transaction size when not in person.
- real-time alerts.
- Monitor account statements weekly. Make this a routine.
- Place a credit freeze on your credit report if you are in the U.S. This restricts access to your credit report and makes it difficult for thieves to open up accounts in your name.
- Place a fraud alert on your credit report – also if you are in the U.S. This lasts 90 days and forces businesses to verify your identity before issuing you credit.
In all of these cases above, if you are able to choose a password, choose one that is complex (more than 12 digits and including uppercase, lowercase, numbers, and other characters), and use a password manager.
Protecting Your Sensitive Information
Sensitive data that you need to protect includes your medical data, tax data, and social security number. There are two surprisingly easy ways of protecting this information.
First, try to avoid creating data about yourself. If it doesn’t exist, you don’t need to protect it. You will frequently find forms that ask for your social security number or equivalent. Most of the forms don’t actually require it. Don’t provide it if it’s not required.
Second, the best way to protect data is to delete it. Once again, if it doesn’t exist, it doesn’t need to be protected. Don’t hoard sensitive data. When you do need to store and protect your sensitive data, encrypt it and use strong device passwords.
Protecting Your Ability to Earn an Income and Protecting Your Reputation
Most of us rely on some type of IT infrastructure to earn a living. Whether you are an architect, photographer or computer programmer, it is important that you secure the systems you use. Here are a few tips to secure your own systems and the services you use:
- If you have a WordPress website, make sure that you have a malware scanner and firewall in place, and look into upgrading your security by using SSL.
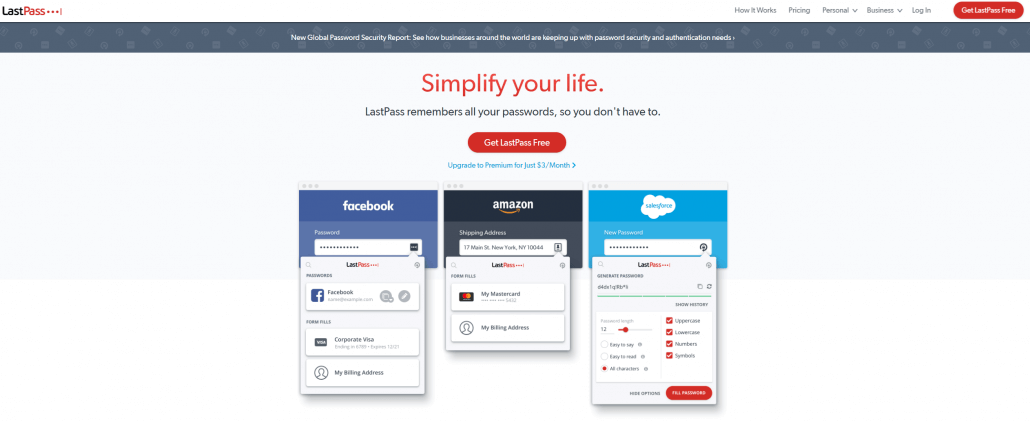
- Use a password manager like Last Pass to automatically store and generate long complex passwords that are different for each system you access.
- Secure your phones, tablets, laptops, and PCs by using disc encryption when available and use complex passwords for device access.
- Avoid adding data to systems that you need or use.
- Enable two-factor authentication on all systems or services you use.
- Keep backup drives in a secure place and destroy sensitive data that you don’t need. Never simply throw backup devices in the trash without either using a secure wiping software or physically destroying them with a large hammer.
Protecting Your Online Reputation
If you use social media, never simply ‘Share’ or retweet someone else’s post until you have fully read it, understood it and also understand any context around it. If you accidentally share something that is highly controversial without fully understanding what you’re sharing, you may find your professional reputation severely damaged.
Secure any social media accounts that you own. If your account is hacked, it may be used for spam which could damage your online reputation.
Secure any websites that you own. If your website is hacked, it will damage your search engine ranking and infuriate your customers if their data is stolen. This can have a severe impact on your reputation. If you use WordPress, install Wordfence which will help prevent a hack.
When installing apps on your smartphone, avoid apps that are aggressively viral. Some apps gain access to your contacts list and can SMS, private message or email your contacts a message from you that suggests they also sign up for the service.