Ten ways to protect yourself online
Any time you are online you are vulnerable to hackers. Whether you are a sole proprietor or a massive corporation like Sony, your chances of being hacked, scammed, or infiltrated in some way, are unfortunately about the same. Hackers can steal your credit card numbers, tax records and passwords, erase your hard drive, disable your entire computer, and even use your built-in webcam or microphone to spy on you. The most complete way to protect yourself online would be to get offline and disconnect yourself immediately, but that solution is no longer an option for any of us.
To protect yourself online, you should take these 10 steps very seriously:
1. Fortify your passwords
Don’t reuse your passwords. If an attacker gets your password she might try it on all of your accounts. This means that a given password is really only as secure as the least secure service where it’s used. Use a single master password or passphrase along with a password manager like LastPass. Choose strong passwords – short passwords of any kind, even totally random ones like nQ\m=8*x or !s7e&nUY are not strong enough today.
2. Use a password manager
Check out LastPass. This is what I use. There’s a free version that syncs between devices but doesn’t allow you to sync with your mobile phone. The premium version costs just $12/year!
3. Secure your security questions
Beware of security questions. Honest answers to many security questions are often publicly discoverable facts. If you do use factual information in the security questions, make them more secure by adding numbers and other characters. Your cat Fluffy can be F1uff7 instead.
4. All HTTPS all the time
HTTPS will encrypt any stream of data between you and the service, ensuring that anyone using Firesheep or a packet sniffer on a (usually public) Wi-Fi network can’t glean your login data. Never work at a coffee shop or other public wi-fi without it.
5. Turn on Two-Step Verification
Facebook and Google both offer the option of 2-Step authentication when you login, meaning you have to enter a secondary pin number which is generated and/or texted to your phone. It’s a complete and utter pain in the ass whenever you’re logged out, but it’s also a pretty safe guarantee that no one will be getting into your account without a heavy-duty targeted attack.
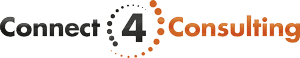
6. Use a secret email address
Publicly available information is the first way a hacker can get their foot in the door. Few things are tossed around more casually than an email address. Don’t give potential hackers a starting point, especially if you use the same login info across multiple sites (which you shouldn’t be doing in the first place!). Instead, create an email address that as few people know about as possible that you use only for account log-ins.
7. Set up login notifications
Facebook will allow you to receive a text message anytime an unrecognized IP address logs in to your account. You may not prevent a hack, but if you act quickly enough, you can remotely log them out and re-secure your account before they get their hands too deep into your business. Gmail is also set by default to alert you if it notices anything particularly strange with your login activity.
8. Put passwords on your devices
This is a no-brainer and should not require explanation. All of your phones, tablets, laptops, and desktops should have a password.
9. Don’t save your credit card information in your browser
Another no-brainer.
10. Keep an offline backup
Just in case your online backup provider is ever hacked, it’s probably a good idea to have your most important documents backed up using a physical hard drive connected to your computer.
11. Don’t link your accounts
Facebook sign-on certainly makes life easy for you, but imagine what happens when someone steals the phone that doesn’t have a password or hacks your password on your computer.
12. Use email wisely
Email is a great way to keep in touch with friends and family, and as a tool to conduct business. Even if you have good security software on your PC, however, your friends and family might not have the same protection. Be careful about what information you submit via email. Never send your credit-card information, Social Security number, or other private information via email.
Conclusion
Those of you who are very perceptive will note that I couldn’t resist and actually gave you 2 extra tips for protecting yourself online. Data shows that a blog post titled “ten ways to protect yourself online” will do better than the same post titled “twelve ways to protect yourself online”. If I had to hone in on one or two particularly important ways to protect yourself online, I would pick number 1/2 – fortify your passwords/use a password manager and number 12 – use email wisely as the most important ways to protect yourself online.
Do you all agree with me? Did I miss anything?